The hybrid workplace model—combining remote and in-office work—has become a permanent fixture for many organizations in Egypt and beyond. While it offers flexibility and productivity gains, it introduces unique physical security challenges. Offices with variable occupancy are more vulnerable to unauthorized access, theft, and overlooked risks. In 2025, effective corporate security requires adapting traditional measures to this fluid environment.
This comprehensive guide outlines proven best practices for maintaining robust physical security in hybrid workplaces, drawing from evolving industry standards and real-world implementations. By addressing access control, monitoring, personnel management, and integration, organizations can protect assets, employees, and operations without compromising the benefits of hybrid work.
Understanding the Hybrid Workplace Security Landscape
Hybrid offices often operate at partial capacity, with employees rotating between home and office. This creates inconsistent human presence, making facilities more susceptible to intrusions during off-peak hours or days. Traditional security models assuming full occupancy no longer suffice.
Key challenges include managing dynamic access needs, monitoring underutilized spaces, and integrating physical security with cybersecurity protocols. Successful strategies treat the hybrid office as a flexible ecosystem requiring adaptive, layered protection.
1. Implement Flexible and Intelligent Access Control Systems
Access control is the foundation of hybrid workplace security. Fixed schedules are obsolete when employee presence varies daily. Explore our access control solutions for tailored implementations.

Best Practices for Access Control:
- Adopt mobile credentials and biometric authentication for seamless, secure entry without physical keys or cards.
- Use time-based and role-based permissions that automatically adjust according to scheduled office days.
- Implement multi-factor verification for sensitive areas like server rooms or executive offices.
- Integrate visitor management systems with pre-registration to track external access effectively.
- Regularly audit access logs to identify unusual patterns or dormant accounts.
These measures ensure only authorized personnel enter during variable occupancy while maintaining detailed records for compliance and investigation.
2. Enhance Monitoring and Surveillance Coverage
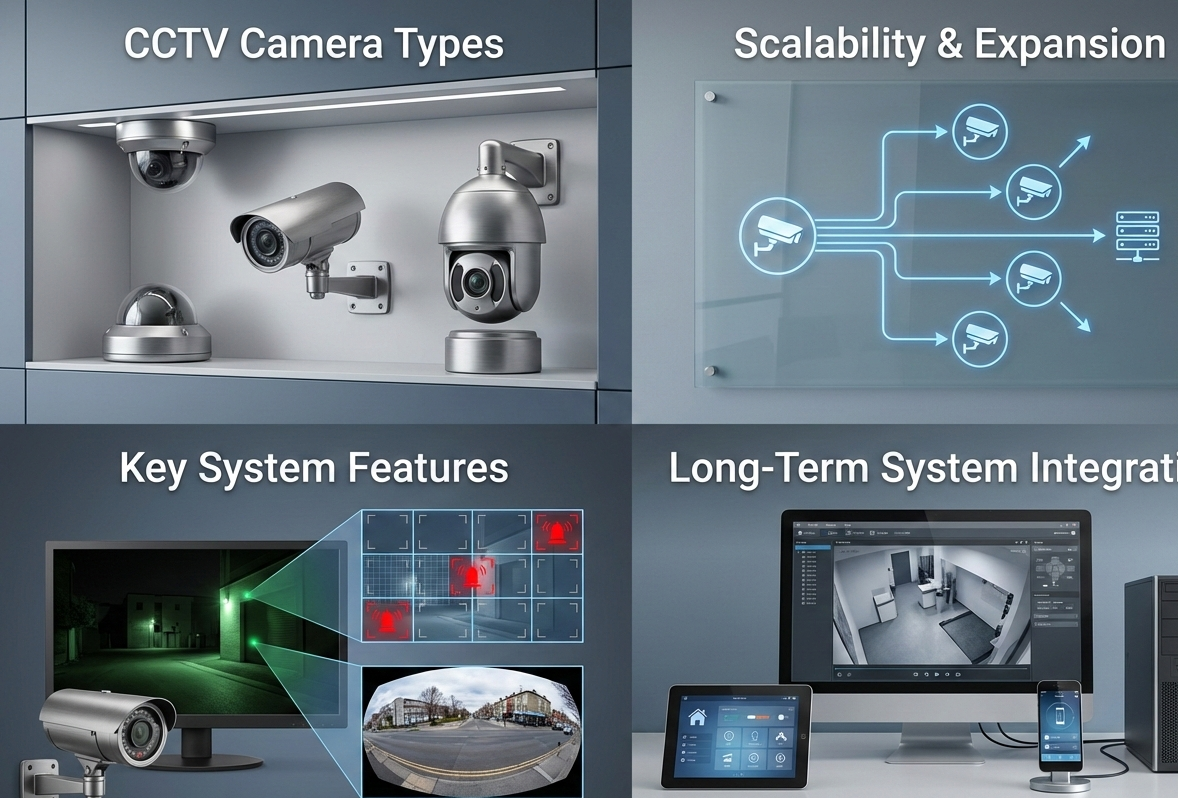
Reduced on-site presence means greater reliance on technology for continuous oversight. CCTV systems must cover all areas, including those typically occupied during standard hours. See our CCTV surveillance services for advanced options.

Key Surveillance Strategies:
- Deploy high-resolution cameras with AI analytics to detect unusual activity in low-occupancy periods.
- Position cameras strategically in parking areas, entrances, common spaces, and corridors.
- Integrate motion-triggered recording to conserve storage while capturing relevant events.
- Ensure 24/7 remote monitoring capabilities with alerts to security teams.
- Regularly maintain and update systems to prevent vulnerabilities.
Advanced analytics can flag anomalies such as prolonged loitering or unauthorized access attempts, enabling proactive response rather than reactive investigation.
3. Adapt On-Site Security Personnel Deployment
Static guarding remains essential but must be optimized for hybrid patterns. Full-time presence may not be necessary daily, but strategic coverage is critical.

Effective Personnel Management:
- Schedule guards based on occupancy forecasts and high-risk periods.
- Combine static posts at entrances with mobile patrols covering multiple floors.
- Train personnel in hybrid-specific protocols, including remote coordination.
- Use rapid response units for immediate support during incidents.
- Implement regular security briefings aligned with weekly office schedules.
This flexible approach maintains visible deterrence while optimizing resource allocation.
4. Strengthen Perimeter and Facility Protection
Hybrid offices often have extended periods of low activity, increasing perimeter vulnerability.

Perimeter Security Comparison:
| Traditional Approach | Hybrid-Recommended Upgrade |
|---|---|
| Fixed guards at entrances | Mobile patrols + AI alerts |
| Basic fencing | Anti-climb + sensor integration |
| Standard lighting | Motion-activated LED + solar options |
| Manual vehicle checks | License plate recognition |
Perimeter Security Recommendations:
- Install robust fencing, lighting, and perimeter alarms with immediate notification.
- Secure all entry points, including loading docks and emergency exits.
- Conduct regular perimeter patrols, especially during off-hours.
- Integrate vehicle access control with license plate recognition.
- Establish clear zones separating public and restricted areas.
5. Foster a Security-Conscious Culture
Employee awareness is crucial in hybrid environments where informal oversight is reduced.

Building Security Awareness:
- Provide regular training on reporting suspicious activity and proper access procedures.
- Implement clear policies for desk clearing and device security when leaving workstations.
- Encourage "see something, say something" reporting culture.
- Conduct periodic security drills tailored to hybrid scenarios.
- Use digital signage and communications to reinforce security messages.
6. Integrate Physical and Digital Security Measures
Hybrid work blurs the line between physical and cyber threats. A unified approach is essential.
Establish joint protocols between physical security teams and IT departments. Integrate access control with network authentication, ensuring physical entry corresponds with digital access rights. Use unified incident reporting systems that capture both physical and cyber events. For integrated solutions, visit our integrated security systems page.
Conclusion: Building Resilient Hybrid Security
Securing hybrid workplaces in 2025 requires moving beyond traditional models to embrace flexible, integrated, and intelligent approaches. By combining adaptive access control, enhanced monitoring, optimized personnel deployment, and strong cultural awareness, organizations can maintain high security standards while supporting modern work practices.
The most successful implementations view security as an enabler of hybrid work rather than a restriction, creating environments where employees feel safe and productive regardless of location.
Key Implementation Steps:
- Conduct a comprehensive hybrid security assessment
- Upgrade to flexible access and monitoring systems
- Align personnel deployment with occupancy patterns
- Build cross-departmental security coordination
- Establish ongoing training and review processes
At EGY Blanco for Security, we specialize in designing and implementing hybrid workplace security solutions tailored to your organization's specific needs and schedules.