The private security industry in Egypt stands at a crossroads While the sector has grown significantly—driven by real estate expansion, corporate demand, and major events—many security companies still operate with paper-based systems, manual scheduling, and reactive incident reporting. In 2026, this traditional approach is no longer sustainable. According to Gartner's 2026 security trends analysis, security leaders are navigating uncharted territory as AI and digital tools converge with traditional operations. Companies that fail to digitize risk becoming obsolete.
Digital transformation in private security is not about replacing guards with machines—it's about empowering security personnel with tools that make them more effective, providing clients with real-time visibility, and enabling data-driven decision-making. From workforce management software to integrated Security Operations Centers (SOCs), technology is reshaping every aspect of how security companies operate. At EGY Blanco Security, we've embraced this transformation, and this guide shares insights for companies looking to make the leap. Explore our Security Management Solutions to see how we implement these technologies.
1. The Challenges Facing Traditional Security Companies
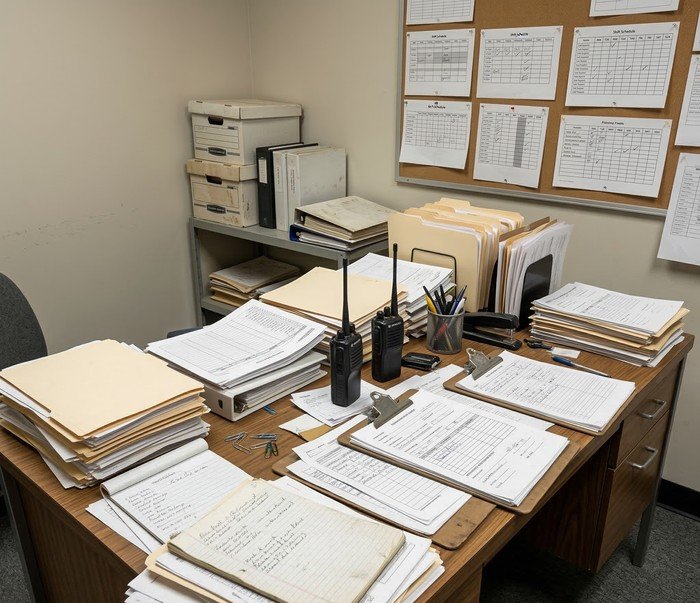
Before understanding the solutions, it's essential to recognize the pain points that plague traditional security operations. Industry research indicates that a significant percentage of security companies still rely on manual processes that introduce inefficiency and risk.
Common Pain Points:
- Paper-based reporting: Incident reports, patrol logs, and attendance records still on paper, leading to data loss and lack of accountability.
- Manual scheduling: Spreadsheet-based shift planning that doesn't account for guard skills, locations, or real-time changes.
- No real-time visibility: Clients have no way to confirm if guards are actually on-site and patrolling as required.
- Delayed incident response: Communication gaps between guards, supervisors, and control rooms slow down emergency response.
- Lack of data insights: No historical data to analyze patterns, optimize deployments, or prove value to clients.
These challenges not only increase operational costs but also damage client trust and retention. Forward-thinking companies are addressing them through digital transformation.
2. Workforce Management Software: From Paper to Platform
The foundation of any digital security operation is robust workforce management software. These platforms replace spreadsheets and paper logs with centralized systems that manage every aspect of guard operations. According to ISO 18788 standards, effective security operations require documented procedures and continuous improvement—capabilities that digital systems enable.

Key Features of Modern Workforce Software:
- Intelligent Scheduling: Algorithms that match guards with shifts based on certifications, location proximity, and historical performance.
- Mobile Guard Apps: Guards receive assignments, submit reports, and verify attendance via smartphone apps with GPS tracking.
- Biometric Attendance: Fingerprint or facial recognition to eliminate buddy-punching and ensure accurate payroll.
- Performance Analytics: Dashboards showing guard punctuality, incident response times, and client satisfaction metrics.
- Digital Incident Reporting: Guards can submit detailed incident reports with photos directly from mobile devices, instantly available to supervisors and clients.
Companies implementing these systems report 30-40% reduction in administrative overhead and significant improvements in service quality. Our Mobile Patrol Security service leverages these technologies to provide clients with verified patrol data.
3. Guard Tour Monitoring: Verifying Presence and Performance
One of the most significant advancements in security technology is automated guard tour monitoring. Gone are the days of clipboards and mechanical watchman clocks. Modern systems use NFC tags, QR codes, and GPS to verify guard presence at designated checkpoints.

How Modern Guard Tour Systems Work:
- NFC/QR Checkpoints: Guards tap their mobile devices at designated locations, creating an immutable record of their patrol.
- GPS Tracking: Real-time location tracking shows supervisor exactly where guards are at all times.
- Missed Checkpoint Alerts: If a guard misses a scheduled checkpoint, supervisors receive immediate notifications.
- Patrol Reports: Automated reports sent to clients showing completed patrols, times, and any observations.
The ASIS International guidelines emphasize the importance of verified patrols as a core component of physical security operations. These systems provide the verification that clients increasingly demand.
4. Security Operations Centers: The Digital Nerve Center
The evolution from fragmented monitoring to integrated Security Operations Centers (SOCs) represents a quantum leap in security capabilities. A modern SOC consolidates CCTV feeds, access control alerts, guard communications, and incident reports into a single dashboard. Recent case studies demonstrate the power of this approach—Banque Misr's centralized SOC now monitors over 900 sites across Egypt in real-time, with operators able to respond immediately to incidents.

SOC Capabilities for Security Companies:
- Centralized Video Monitoring: Aggregating feeds from multiple client sites into a single view, with AI analytics flagging anomalies.
- Access Control Integration: Real-time visibility into who is entering and exiting facilities, with automated alerts for unauthorized access.
- Guard Tracking: Live map showing all deployed guards and their status.
- Incident Management: Digital incident tracking from initial alert through resolution, with complete audit trails.
- Emergency Communication: Two-way communication with guards in the field during incidents.
For security companies, establishing a SOC—even a virtual one—enables them to offer premium monitoring services to clients. Our Emergency Response & Rapid Intervention Units are coordinated through advanced SOC capabilities.
5. Client Mobile Applications: Transparency as a Service
One of the most powerful digital transformation tools is the client-facing mobile application. These apps give clients unprecedented visibility into the security services they're paying for, transforming security from an opaque expense into a transparent, value-generating partnership.

Features of Modern Client Apps:
- Guard Verification: See exactly which guards are on-site, when they arrived, and their current status.
- Incident Reports: Immediate access to incident reports with photos and resolution status.
- Performance Dashboards: Historical data on patrol completion rates, response times, and security metrics.
- Direct Communication: Secure messaging with security supervisors and control room operators.
- Digital Documentation: Access to security plans, emergency procedures, and compliance documents.
Security companies offering these apps report significantly higher client retention rates and the ability to command premium pricing. The transparency builds trust and demonstrates value in concrete terms. Learn about our approach at EGY Blanco Security.
6. Data Analytics: From Reporting to Prediction
The data generated by digital security systems is a goldmine for continuous improvement. Advanced analytics can identify patterns, predict risks, and optimize resource allocation. According to the World Economic Forum's 2026 Global Cybersecurity Outlook, 78% of CEOs at highly resilient organizations say third-party and supply-chain dependencies are their biggest challenge—data analytics helps address this by providing visibility.
- Incident Trend Analysis: Identify patterns in incidents by time, location, and type to proactively deploy resources.
- Guard Performance Metrics: Objective data on punctuality, patrol completion, and incident response for performance management.
- Cost Optimization: Analyze deployment data to right-size staffing levels without compromising security.
- Predictive Risk Modeling: Use historical data to predict high-risk periods and locations, enabling proactive measures.
7. Integration with Client Systems: Creating a Unified Security Ecosystem
The most advanced security companies don't operate in isolation—they integrate their systems with client infrastructure. This creates a seamless security ecosystem where data flows between the security provider and client systems.
- CCTV Integration: Security company SOC can access client camera feeds (with permission) for enhanced monitoring.
- Access Control Integration: Guard tour systems can verify that doors are properly secured during patrols.
- Alarm System Integration: Alarms triggered at client sites automatically create incidents in the security company's system.
- API Connectivity: Modern security platforms offer APIs that enable custom integrations with client systems. Explore our Integrated Security Solutions.
8. Challenges and Barriers to Digital Transformation
Despite the clear benefits, many security companies struggle with digital transformation. Common barriers include:
- Cost of Implementation: Software licenses, hardware, and training require upfront investment that smaller companies may struggle to afford.
- Resistance to Change: Guards and supervisors accustomed to paper-based processes may resist new technology.
- Digital Skills Gap: Many security personnel lack the digital literacy to use advanced systems effectively.
- Cybersecurity Concerns: Moving operations online introduces new cybersecurity risks that must be managed. AI-powered cybersecurity solutions are becoming essential for protecting digital security infrastructure.
Overcoming these barriers requires leadership commitment, phased implementation, and ongoing training. Starting with pilot projects can demonstrate value and build momentum.
9. The Future: AI, Automation, and Beyond
Looking ahead, the digital transformation of security companies will accelerate. Gartner predicts that by 2026, "agentic AI"—AI systems that can take autonomous actions—will become widespread, creating new capabilities and new governance challenges. Security companies that embrace these technologies will gain significant competitive advantages.
- AI-Powered Scheduling: Algorithms that optimize guard schedules based on real-time data and predictive analytics.
- Automated Video Analysis: AI that continuously monitors CCTV feeds and alerts guards to potential incidents.
- Digital Twins: Virtual replicas of client facilities that enable simulation and optimization of security operations.
- Predictive Threat Detection: Systems that identify potential threats before they materialize based on pattern analysis.
10. Conclusion: Embracing the Digital Future
Digital transformation is no longer optional for private security companies in Egypt. Clients increasingly expect real-time visibility, verified performance data, and seamless integration with their own systems. Companies that embrace these technologies will thrive; those that don't will struggle to compete.
At EGY Blanco Security, we've made digital transformation central to our service delivery, and we're ready to help other security companies on their journey. Contact our team to learn how we can support your digital transformation initiatives.
📋 Digital Transformation Checklist for Security Companies
- Assess current operations and identify pain points
- Research and select workforce management software
- Implement guard tour monitoring with mobile apps
- Develop SOC capabilities (physical or virtual)
- Create client-facing portal or mobile app
- Establish data analytics and reporting processes
- Train staff on new systems and processes
- Plan for integration with client systems
- Implement cybersecurity measures for digital infrastructure
- Continuously review and optimize based on data





